Forums › Community › SSL vulnerabilities – WikiLeaks › Reply To: SSL vulnerabilities – WikiLeaks
Pedro
Again, thank you for your reply.
SSL can be logged by somebody in a privileged position: AV scanners, corporate firewalls, Superfish-style vulnerabilities to name but a few.
SSL on its own isn’t used to protect world secrets; it’s used in conjunction with other protocols – normally E2E encryption in addition to SSL.
I’m not advocating you roll your own encryption; that’s a terrible idea even for an experienced cryptographer. I am suggesting that you consider an additional, peer-reviewed protocol like PAKE, in addition to SSL.
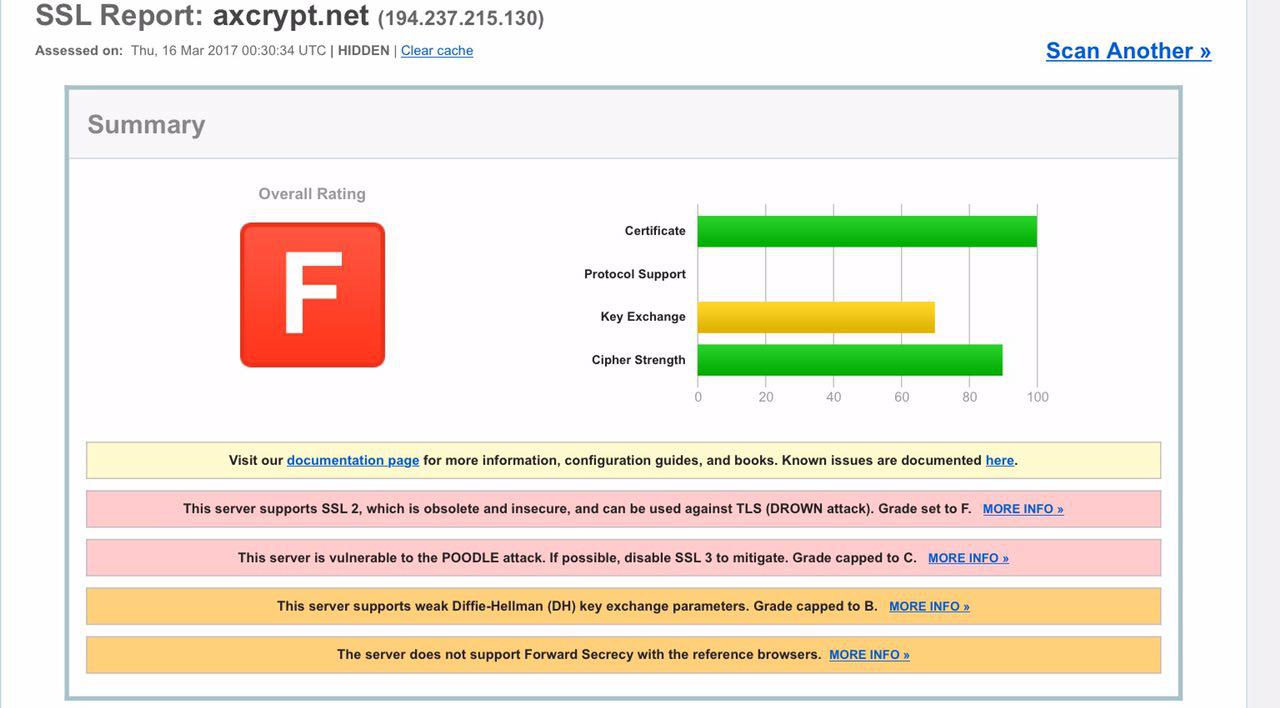
Regarding this site, take a look at your Qualys report. The site scores an F – the lowest possible. A+ is the best possible mark.