This topic contains 64 replies, has 3 voices, and was last updated by Anonymous 3 years, 7 months ago.
-
AuthorPosts
-
Hi,
AxCrypt does zip-style compression before encryption…
AxCrypt 1 & 2 are designed for the same basic use-case, it’s just that AxCrypt 2 has evolved based on input and feedback for more ease of use, and wider usability (sharing). They work the same, the only difference is that the AxCrypt 1 checkboxes “Remember this for encryption” and “Remember this for decryption” are “always checked” (they don’t exist, but in principle) in AxCrypt 2, and instead we use the screen saver or similar to clear the password memory. You should *always* lock your computer when you walk away from it. If you don’t it doesn’t matter what I do with AxCrypt, you should consider your system and security as compromised.
BrianBen Langton
I would like to apologize for the tone of my initial post […] I highly recommend having some sort of document, posted prominently on your website, to help transition users of AxCrypt 1 to AxCrypt 2
I don’t think it was your initial post that he was referring to. Anyhow it doesn’t matter now :-).
A colourful infographic would be a neat idea as a visual representation is often clearest.
RaymondLC92
Ah I hadn’t thought of cloud transfers, that’s not something I engage in often and when I do I usually need compression. In such cases I usually use an encrypted archive (i.e. 7zip).
7-Zip has some problems with its encryption, discussed elsewhere on this forum. It’s not a bad piece of software but there are better alternatives. It’s not insecure under most situations but there are outstanding issues with it (discussed in-depth on their forums).
Use 7-Zip for your compression and then use GPG (or AxCrypt) for the resulting archive.
I can see AxCrypt being very useful for encryption of files uploaded to DropBox, OneDrive, etc.
I automatically synchronise my cloud folders but only content with an .AXX extension will be uploaded. By doing this no unencrypted data ever touches the cloud, and, because I’m working with multiple files AxCrypt 2 saves time on entering the password, decrypting and then re-encrypting compared with the laborious (and more human error prone) AxCrypt 1.
Bitlocker (or other FDE) is like locking down a building at night but AxCrypt was like locking my office door behind me and only unlocking it when I needed it open.
That’s not a good analogy because you’re describing how AxCrypt 2 works.
- You shutdown (that clears your AxCrypt 2 encryption key)
- Your computer switches off (that clears your BitLocker key)
When you restart your computer or sign out of AxCrypt or lock your desktop environment or put your computer to sleep or hibernate your computer or your screensaver starts then AxCrypt 2 clears your encryption key.
Actually AxCrypt 2 works in virtually the same way as AxCrypt 1 except it’s more convenient. The only argument you can make against AxCrypt 2 is if your computer is hacked whilst you’re logged into AxCrypt 2 an attacker could steal your password but that same argument applies to AxCrypt 1 (where a criminal would capture all your passwords over time and/or data).
Stephen@RaymondLC92
7-Zip is riddled with various vulnerabilities because the only developer is a sole Russian guy with no viable funding model and not enough time on his hands. It’s very sad because the compression of 7-Zip is fantastic but nobody wants to fund his hard efforts.
Cisco found multiple severe vulnerabilities which, amongst other things, undermined the security of 7-Zip. These flaws were fixed (in 16.04 and 17.00 (beta)) but many others security problems remain and not all have been disclosed.
There is an abundance of commercial cracking software available for Zip/7-Zip files because the original format [ZipCrypto] was not designed with security in mind. Subsequent implementations have improved but recovery can still be effectuated by those in the know.
AxCrypt 1 and 2 were designed with the same use-cases: file level encryption. The fact AxCrypt 2 remembers your password is irrelevant and Brian has explained some of these.
If you’re going to keep an archive then either use PGP or use a BitLocker Virtual Hard Drive. The problem you’ll have is synchronising to the cloud because of data de-duplication and a very large file (not individual files) which needs to be uploaded on the fly. You said you don’t utilise cloud services so a Virtual Hard Drive will serve you better than 7-Zip. Individual files can be encrypted with AxCrypt.
You need to configure virtual hard drives correctly using the new block cipher mode with a non-escrowed external recovery key and augmented key length if you want top security. Properly configured it surpasses what is currently offered by VeraCrypt and is more stable in the Windows environment.
You spoke about being an “advanced user” but from your posts you come across as an novice user who knows how to use basic out-of-the-box encryption. It’s good that you’re interested but with computer security you’ve got to realise that unless you really understand the subject (and all its pitfalls) you’re likely to fail when presented with too many options. This is not the same as calling you stupid (or the “lowest common denominator” as you suggested AxCrypt’s user-base must be); it’s recognising that you don’t have the cryptographic, mathematic and engineering skills to make an informed choice.
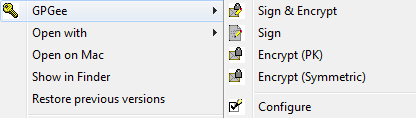
About GPG4Win you can symmetrically encrypt from the GUI via using the GPGee extension. I’ve put a picture below. GPG is extremely secure software but the defaults aren’t good because they’re designed to be backwards compatible with older versions and to conform to the PGP standard. Therefore you’ve got to know what you’re doing to use it safely. There is lots of good technical information out there.
StephenAnother useful article for you.
https://security.stackexchange.com/questions/100650/how-secure-is-7z-encryption
There is cracking software for 7-Zip which allows me to crack an archive (with any key-length) in under 60 minutes. This is not because I’ve cracked AES (I haven’t) but because it’s badly implemented in 7-Zip.
RaymondLC92You spoke about being an “advanced user” but from your posts you come across as an novice user who knows how to use basic out-of-the-box encryption.
It’s all about what you’re trying to protect and how important it is. Your shot at me aside, I’ve never had an encrypted file stolen. All of my most important data is within VeraCrypt VHDs. I can prep one for you to break open but I think you’ll be busy for quite some time.
This is not the same as calling you stupid (or the “lowest common denominator” as you suggested AxCrypt’s user-base must be); it’s recognising that you don’t have the cryptographic, mathematic and engineering skills to make an informed choice.
Again, to assume this of everyone using your product is foolish, provide good defaults but don’t just hide away options. Kaspersky did this when it removed it’s “Advanced options” and caused a great number of configuration issues.
Subsequent implementations have improved but recovery can still be effectuated by those in the know.
It’s sufficient to keep your average nobody from reading them, if you’re going to share files you’re probably going to use some form of public key cryptography anyways (as you’ll still need to be able to securely share the key). When I use the cloud I’m usually transferring files for myself (usually to a machine that isn’t mine).
You seem desperate to be the maximum amount of secure at all times, yet you use software that hasn’t even been audited. You should realize that you’re never safe it’s all a matter of how unsafe are you comfortable with. AxCrypt is open-source but that doesn’t make it secure, go ask OpenSSL.
I don’t operate on the assumption that something is secure, I only expect that it’s secure enough to make it not worth the hassle. Perhaps someone out there really does desperately want the reports I wrote for my University courses. Then again, given that they’ve long become useless to me I suspect that 7zip was probably just fine for that information. Sure seems to have been effective at keeping the average person from cheating off of me, though I imagine there are many people who could break it on the ready.
Could I use 7zip to archive it, and then use GPG to encrypt it? Probably, but why complicate a simple transfer the information isn’t that particularly important (especially when I know I can download portable 7zip should the machine not have it). I think AxCrypt (particularly v1) is fantastically convenient, but I don’t think it’s “secure” though I admit it’s probably “Secure enough” for what I used it for.
My backdoor is a pane of glass with a tiny latch on it, is it “Secure”? No, but it’s enough to keep your average person from just waltzing in.
StephenI am not an employee of AxCrypt and it’s not my software or my product.
This is a user forum; Svante works for AxCrypt – nobody else on this forum does.
Nobody has said any software is absolutely safe and nobody is taking “shots” at you.
Nobody is desperate to be perfectly safe. Instead they’re suggesting reasonable alternatives – e.g. GPG if you’re dissatisfied with AxCrypt 2.
I think this discussion has run its course. People have eloquently explained the situation to you and if you’re still unhappy with AxCrypt 2 then vote with your feet. You don’t need to repeat yourself ad nauseum.
RaymondLC92I think this discussion has run its course.
Agreed, I think the conversation has been finished for quite some time and was fully concluded with Ben’s statement on the previous page regarding explaining that some V1 users may not feel at home with v2.
We can call it closed.
RobertMHello, Stephen.
You state that, “There is cracking software for 7-Zip which allows me to crack an archive (with any key-length) in under 60 minutes.” That is a remarkable claim requiring remarkable proof! Would you mind demonstrating this, as you apparently did with a BCA file? I don’t ask this to be contentious or as a personal challenge. I’ve read of vulnerabilities with 7Zip but you are describing encryption that is essentially worthless.
Here is an encrypted 7z file —->> https://1drv.ms/u/s!AgVhuW8u-GbEhFAZrZ7GTyIzKomL
Thanks!
HjalmarThat is a remarkable claim requiring remarkable proof! Would you mind demonstrating this, as you apparently did with a BCA file? I don’t ask this to be contentious or as a personal challenge. I’ve read of vulnerabilities with 7Zip but you are describing encryption that is essentially worthless.
It’s not just Steven who can crack these files – anybody with a sufficiently powerful GPU rig can!
Theoretically it should take longer than the life of the universe to crack AES but 99/100 it’s not how strong the algorithm is but how developers implement it which determines whether the encryption can be broken or not.
RaymondLC92 talked about AxCrypt and auditing. Audits are worthless in the long term because they’re only valid on the date of of the audit and when using exactly the same version. TrueCrypt was partially audited but the project closed down for mysterious reasons. Various developers, including VeraCrypt took over, and promised to fix the minor issues discovered in TrueCrypt.
Every time a new feature is added to any software or when a feature is removed or something is changed in the source code it opens a window of opportunity for a bug to inadvertently/intentionally introduced. A cautious person would only use TrueCrypt despite its minor vulnerabilities because of the error potential. VeraCrypt is substantially improved but uses a lot of untested code.
We had a member of staff who had a number of encrypted files on our server. We weren’t in a position to get the password/s from him as he’d sadly died in a car crash. We stopped allowing individual password-based encryption after this and insisted on public key encryption (key sharing).
Many of his files were MS Office documents and spreadsheets and the remainder were 7-Zip archives. Most of his MS Office files weren’t cracked (a handful were) but all his emailed 7-Zip files were returned to us decrypted within 24 hours. They didn’t give us a password but they supplied his files instead.
This points to a serious breach of 7-Zip’s security but that doesn’t equate to it being useless. It’ll stop a casual snoop which is what it’s designed for. Those people who can afford to pay to have the files cracked would similarly be in a position to have their target’s system/s hacked which makes encryption useless as other people have commented. It’s much more beneficial for a target system to be hacked and gain a ‘live stream’ of everything instead of ‘fire-fighting’ by having to decrypt archives afterwards.
I don’t know whether Steven will see your message but cracking archives for the fun of it/to prove a point is time consuming and costly. He has linked to commercial recovery solutions if you disbelieve him and there are many people out there who have used that software with success.
RobertMHello, Hjalmar.
It’s not that I disbelieve Stephen, it’s just that claiming the ability to break an encryption in an hour or less is an extraordinary claim (in my opinion). I don’t have a horse in this race and it’s no skin off my nose if 7Zip AES is weak.
I have, in fact, read a number of articles about weaknesses in 7Zip’s AES implementation, but only in this forum have I read claims of actually being able to crack the encrypted files, regardless of password length.
BrianI’m one of the earlier contributors before this topic went off tangent somewhat.
I too have personal experience of breaking into 7Z files. The three tools Stephen links to are all effective. Some take longer than others but under 60 minutes is realistic. I use 7Z but am under no illusions as to how secure it is. Cryptographers like Matt Green have lectured about the insecurity of the format.
One thing that is important which seems to have been forgotten is that if you store lots of files in a big VeraCrypt container all it takes is for the container to be partially damaged and all the data becomes inaccessible. That’s one of the major downsides about container-based encryption. Bit rot also contributes towards damaged containers so it makes backups imperative. At least with file-based encryption (like AxCrypt) the worse that can happen is that you lose access to just one file in the event of damage.
Jack C.I prefer AxCrypt v1 because it’s intuitive to work on individual files vs. a container concept with spatial vagueness.
Also, I often send encrypted files to people (family) who aren’t “into it,” but we have an understood shared password (or hints for alternates) and it works well for semi-reluctant recipients.
Hello Jack C,
Thank you for your input!
I’d like to know more about what gives you the impression that version 2 has “a container concept with spatial vagueness“. Obviously we’re doing something wrong here. AxCrypt 2 works just like AxCrypt 1 – it encrypts individual files, and nothing else. It does have a feature where it monitors folders for files to encrypt, perhaps this is causing the confusion.
We really think the shared key feature works better for sending encrypted files to friends and family, while still maintaining a reasonable security model. Using “understood shared password (or hints for alternates)” is so weak I don’t really see the point at all of going through the extra effort of using a strong encryption tool with such a weak security model. I’d recommend attaching an informative text just stating that this content is private, and anyone but the legitimate reader really should not peek. I think it’ll provide stronger protection, really!
From an AxCrypt point of view, we’d like to discourage such use of the product, since when the data is leaked due the weak key management we’ll probably get the blame while in fact it’s just how it’s (mis-)used that is the real problem. We’d like AxCrypt to be really easy to use, and hard to misuse.
Jack C.I agree it’s not a true “container” subject to being corrupted and losing all files, but it isolates the files in a floating window, which gives aesthetic detachment. I’ve avoided container password apps (like TrueCrypt) for the same reason. A good analogy is that your files are being encrypted in another “room” when they needn’t leave the room in the first place. I know that’s not entirely logical, but so it goes with preferences. Drag & drop isn’t my favored method for encryption. Yes, I could get used to it and still might.
I also want to keep email entirely out of it but know of that bypass trick (a separate topic, really).
I’d also rather use a lot more than one password for the way I use it with family members and others who put no real effort into setting it up on their end. Not super secret stuff, just email privacy. For myself, I use stronger passwords with a few variants of a base password.
I use an offline password manager to keep track of all custom passwords. Altogether, I’ve used a dozen+ different passwords with AxCrypt over the years and only once forgot one that was a test quickie.
Jack C.Bottom line is that I’d rather keep the ability to use more than one password whenever it feels necessary, which is echoed by others in this thread. I also sometimes use 7-Zip for encryption in email when I know the recipient doesn’t have AxCrypt installed and would find it a burden to be asked. Yes, there are people like that!
Many people just aren’t “into” this stuff and that’s hard to explain to a programmer who’s steeped in it. For example, my elderly mom is barely aware that she’s even got AxCrypt and my sister only vaguely cares (I put it on both their machines via TeamViewer). When needed every few months, I send mom emails with an .axx file and “open with old-timer code” as an inside clue she can remember. But I don’t want that code to be the same one I use, and she will literally refuse to use a sharing code feature. Computer-phobic to a ridiculous degree.
So, the ability to make passwords on the fly (and still retain a master password) would get people like me on board with 2.0+. If feasible, you could have an “revert to v1 functionality” toggle. With that, I could get used to the new windowed GUI, which I do find superior to most of what’s out there.
-
AuthorPosts

