This topic contains 24 replies, has 2 voices, and was last updated by Svante 7 years, 4 months ago.
-
AuthorPosts
-
Paul ReedI’ve previously used a encryption service called ‘Cloudfogger’ which is very similar to Axcrypt, and one day I tried to decrypt my encrypted files, but it failed due to the project being halted. I had no email informing me to decrypt my data in advance, and the upshot is that I’ve now permanently lost years worth of personal files & messages, with no way to decrypt.
As Axcrypt doesn’t decrypt offline, how can I be assured that this won’t happen again with Axcrypt??
Paul
Hello Paul!
You’re misinformed fortunately. As opposed to Cloudfogger, you can decrypt your AxCrypt files at any time, with or without Internet, and with or without our servers or our business being operational.
As long as you have a copy of the software (and that’s pretty much spread around the Internet by now), and know the original password you can continue to use and decrypt your AxCrypt-encrypted files.
Paul ReedThat’s reassuring, I haven’t installed it yet to test (having being badly bitten by Cloudfogger!), but I did stumble upon this post in the forum, which made me wary.
Thanks for the quick update, I’ll install AxCrypt and give it a try.
Paul
Paul ReedJust trying different scenarios to build my confidence…
I’ve encrypted a folder/contents, uninstalled AxeCrypt, leaving the folder encrypted.
Downloaded AxeCrypt again, switched off wi-fi (to simulate your business not operational) and re-installed Axecrypt.
I was surprised to see that Axecrypt never asked for my email address, as it only asked for the password??Is there a Axecrypt config file hidden somewhere in my OS (Windows 10).
Paul
LucasThere’s another option Paul but it may be too inconvenient.
AxCrypt is designed for encrypting individual files and folders (but not recursively!). If this is what you need then stay with AxCrypt. Unlike Cloudfogger with AxCrypt you can decrypt your data offline. Eventually they plan on building a feature (according to Svante) where you can export your keypair.
At the minute the only scenario where you may lose access to your data is if AxCrypt got hacked* or shutdown AND you also lost your computer which stores your keypair. [*And lost all of their backups (highly unlikely)]
Unless both of these scenarios occur then even if AxCrypt shut down then, as long as you have your computer, you can decrypt all your files. If your computer was stolen BUT AxCrypt remained operational then you’d be able to decrypt your files because you’d be able to download a fresh copy of your keypairs onto your new computer.
The other option is to download a piece of software like VeraCrypt. It’s free and open source, offers extremely secure methods of encryption, is the updated successor to TrueCrypt and does not rely on the cloud. You create a container and drag your files into the container. The problem with this approach is if you store your data in the cloud: if you make an update to one single file then you have to re-upload the whole container to the cloud which may take a long time. It’s a great solution if you’re only keeping files locally but not so good if you’re storing files in the cloud (unless you create an encrypted container for every file).
A commercial alternative is BestCrypt by Jetico which is very similar to VeraCrypt. It has no backdoors, is open source but you have to pay for it. It suffers the same problem as VeraCrypt if you’re using the cloud. It’s used by governments and military forces worldwide.
Paul ReedThanks Lucas, do you know where is the AxeCrypt account key stored? is it a registry entry?
(I’ve seen that it can be exported/imported from the AxeCrypt menu)
Paul
LucasI couldn’t tell you at the moment Paul as I don’t have AxCrypt installed on this system.
However, where it’s stored is largely irrelevant because you can export the secret and key pair. According to this post you can go to: File | Key Management | Export AxCrypt ID Secret and Sharing Key Pair. You should then store those safely (DVD or USB locked in a safe) in the event that AxCrypt gets closed down and your computer gets lost/stolen etc.
<b>However,</b> and I’m not entirely familiar with AxCrypt’s implementation, I’m guessing you would need to re-export the ID secret and sharing key pair in the event that you ever changed your password.
Therefore you have the option to back up the credentials wherever you like; I doubt very much that AxCrypt stores it in the Windows Registry but it may be in the Windows Certificate Manager (certmgr.msc) or the hidden ProgramData folder.
If you’re desperate for an answer to where it’s stored before Svante reads this post you could take a look through the source code: it’ll be buried in there somewhere. If you do find out where, please let me know in this thread.
LucasI’ve just re-read your question Andrew think I may have misunderstood it.
If you’re asking where your email addresss is stored (your offline scenario) it may very well be in the registry or the Program Files folder because uninstalling software normally leaves some remnants.
Or AxCrypt may have embedded your email address into the encrypted file. Again, this would be answered within the source code.
Paul ReedNo, you were correct, as I understand, the axecrypt account key comprises of both public/private keys and some metadata.
I’ve searched the locations that you have suggested without success, and just wading through bitbucket…
All I want to do is completely nuke axecrypt, reinstall it, and be confident that I can recover my data using my backed up keys WITHOUT access to the axecrypt network.
Once bitten, twice shy!
LucasI totally agree. You definitely don’t want a solution which, if taken offline, will result in loss of your data.
I vaguely recall Cloudfogger but I’m not familiar with how it works. That’s why I stick to standards-compliant encryption like AES ZIP encryption which is extremely secure (don’t use legacy ZipCrypto) and will be around for years to come. For individual files that’s not so convenient.
To nuke AxCrypt try uninstalling it from the Control Panel. Then search for and delete ALL of its registry keys. After doing that turn on hidden files in Windows Explorer and go through both Program Files folders. Then check ProgramData. Then check UserData (can’t remember the exact name). Maybe even search your hard drive for any occurrences of AxCrypt.
That should destroy any remnants.
Once you’ve done all of it, reinstall AxCrypt and load it via the Start Menu. If it prompts for your email address then you can be pretty sure it’s been nuked. Then try and load the file and see what happens. It shouldn’t load.
Then import you key pair and AxCrypt ID. I’m guesssing the latter contains your email address hence why you won’t be prompted to enter it!
The reason I say open the encrypted file first is because, if your AxCrypt remnants have indeed been nuked, it’ll refuse to open and will need to download the keypair etc. from the server. That’s why it’d need your email address and password. In the scenario of AxCrypt being closed then you wouldn’t have access to the server, obviously.
If it won’t load the encrypted file, then load your keypair and ID. It probably will only prompt you for your password, assuming your email address is embedded in either the ID or the file. Either way this simulates AxCrypt being shut down because as long as you can access your encrypted files then you’ve got nothing to worry about.
It’ll be interesting to see if that does the trick.
I trust this helps.
LucasMerry Christmas!
Paul, I was speaking with a family member today who had come around for Christmas and he pointed me towards an excellent freeware utility (BCArchive) which is very similar towards AxCrypt 1.7 but it supports a number of encryption algorithms (both symmetric and asymmetric) plus it integrates really well within the Windows Shell.
It also can create a self extracting file if you’re sharing with somebody else.
The software is entirely offline and no registration is necessary.
LucasAn independent review:
http://www.ghacks.net/2013/09/21/bcarchive-create-archives-using-public-key-encryption/
Paul ReedHi Lucas, thanks for that, however I haven’t given up on AxeCrypt yet and if I can remove all traces of it from Windows, to enable me to do the tests I’ve described above, I’m sure AxeCrypt will be my best solution.
Hopefully Svante will point me to where AxeCrypt actually stores keys & metadata.
Best Wishes
Paul
Hi Paul (& Lucas),
I need to correct Lucas on one point. AxCrypt is a password based file encryption utility. The AxCrypt ID key pairs used are for convenience in sharing and managing passwords. You will not lose your encrypted data if you lose your key pair. You can *always* decrypt a file if you have the software and know the password that was used when the file was encrypted.
In order to ‘nuke’ AxCrypt completely, it generally suffices to uninstall it via the control panel. Nevertheless, there are scenarios where some user and configuration data could be left on the computer. AxCrypt uses the following locations:
%localappdata%\AxCrypt in the file system for user data. This is always safe to ‘nuke’, even with AxCrypt installed (temporary decryption is done here, so working files may be deleted if you delete this folder entirely, but the installation as such will not be damaged).
HKLM\Software\AxCrypt
and
HKCU\Software\AxCrypt in the registry for configuration data pertaining to the Explorer integration, and the Windows Installer engine.
(It also adds file some shell integration stuff elsewhere, but that has no impact whatsoever on the ‘nuke’ aspect, and also these are removed during uninstallation).
The standalone version of AxCrypt, which does not require installation, does not use the registry at all but only the %localappdata%\AxCrypt location.
Paul ReedThank you for your reply & patience Svante.
The issue I’m struggling with is that you say;
” you can decrypt your AxCrypt files at any time, with or without Internet, and with or without our servers or our business being operational.” and
” You can *always* decrypt a file if you have the software and know the password that was used when the file was encrypted.”Yet, let’s assume that your business becomes non-operational, then how could we install the software (or run the portable version) to decrypt data, as we would be unable to obtain a 6 digit verification code from your servers?
Of course I realise that it’s unlikely that I wouldn’t have a registered installed copy of your software, BUT that’s more or less what happened with Cloudfogger;
Cloudfogger stopped their servers without anyone knowing, and it was some weeks later when I upgraded to Windows 10 that I reinstalled a ‘local saved version’ of their software, and found that without their servers being operational I couldn’t decrypt my data, and lost everything.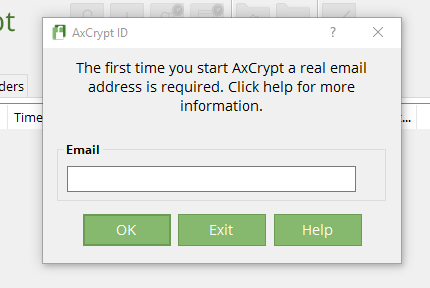
Paul
-
AuthorPosts

