Forums › Help & support › Old Axcrypt file not opening
This topic contains 21 replies, has 2 voices, and was last updated by Svante 7 years, 2 months ago.
-
AuthorPosts
-
AdamI used to use the old Axcrypt on my Windows PC.
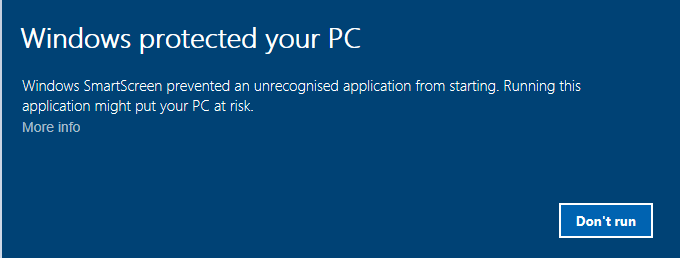
I’ve installed the new Axcrypt but when I went to open one of my encrypted files it gave me this warning message. I’ve pressed More info and there’s no option to run it.
Is there any way I can open my old encrypted Axcrypt file or do I need to install the old Axcrypt again?
I don’t know if it’s a Windows problem or an Axcrypt problem.
Thankyou
Hello Adam,
That’s strange. Windows sometimes displays that message, when we released a new version but we quickly get the reputation needed to avoid. Unfortunately Microsoft has chosen to respect the fact that we’re digitally signed with a proper certificate.
You should be able to run it anyway, under More Info. See here: http://www.howtogeek.com/123938/htg-explains-how-the-smartscreen-filter-works-in-windows-8/ . Do you have a screen shot of the “More Info” screen?
Also, ensure that you downloaded the most recent version of AxCrypt from https://forum.axcrypt.net/ and that the digital signature is correct by checking file properties after download, and select “Digital Signatures”.
AnonymousHi, it’s the self decryptor Axcrypt file that I’m trying to open, not the actual Axcrypt file. The More info shows nothing, it’s blank.
You said that
Unfortunately Microsoft has chosen to respect the fact that we’re digitally signed with a proper certificate.
Did you mean that Microsoft has chosen NOT to respect? I don’t think this applies here anyway because you don’t sign the self decryptor files?
I don’t trust Authenticode because it’s too easily tampered with. There is a version of Axcrypt on the internet which I haven’t installed because my antivirus says it’s not real. It has your certificate but a different date of signing when I compared it to the version of this website.
AdamDo you know why this file is signed by Axcrypt certificate if it isn’t genuine?
I managed to decrypt my self decrypting files on an old Windows 7 computer.
Hello,
First, yes – my bad. Microsoft has chosen NOT to respect the signature.
Secondly – I’m confused. Adam – what was the name of the executable that triggered the first “Windows protected your PC” message. You wrote that it popped up when you tried to open an old file, so I was under the assumption that this happened when you tried to use the new version 2.1 AxCrypt. If, in fact, this was a self-decrypting file i.e. something like “My File-ext.exe” – then it’s entirely possible that the warning comes up. But I still don’t see why you don’t get an option to run anyway.
Now, you write “I don’t trust Authenticode because it’s too easily tampered with“. Really? This is not true at all. Authenticode is a strong digital signature, with quite adequate cryptographic strength. Can you provide a reference to indicate that Authenticode is vulnerable?
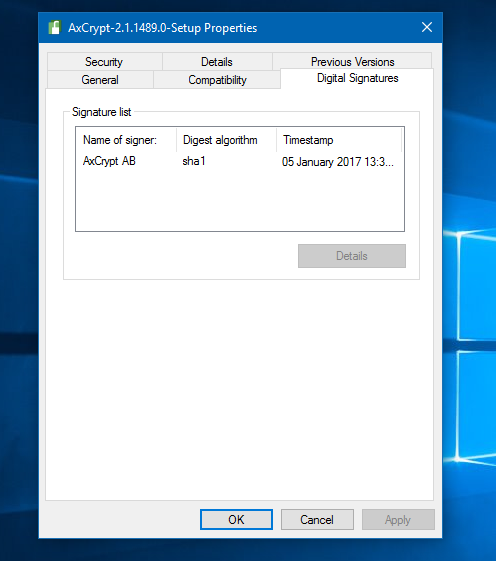
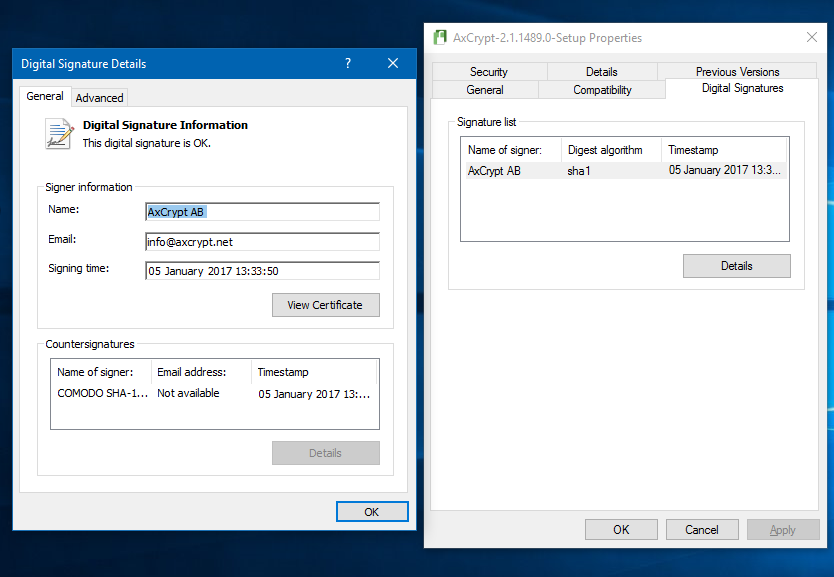
Finally, you refer to “a version on the internet” and send a screen shot with what appears to be a digitally signed “AxCrypt-2.1.1489-Setup.exe” but with a timestamp of January 5, 2017 – and that is indeed wrong.
Can you check the validity of this signature using the ‘Details’ button please and send a screen shot. Also, I’d very much like a copy of that file as well a link to the source of it.
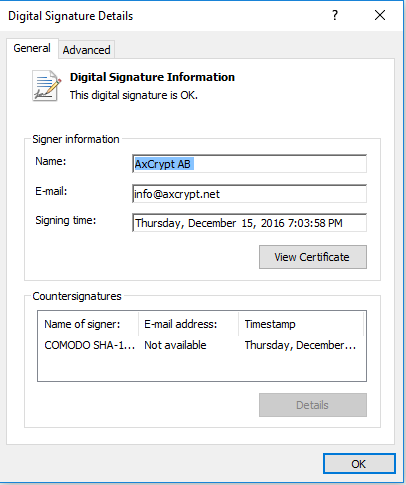
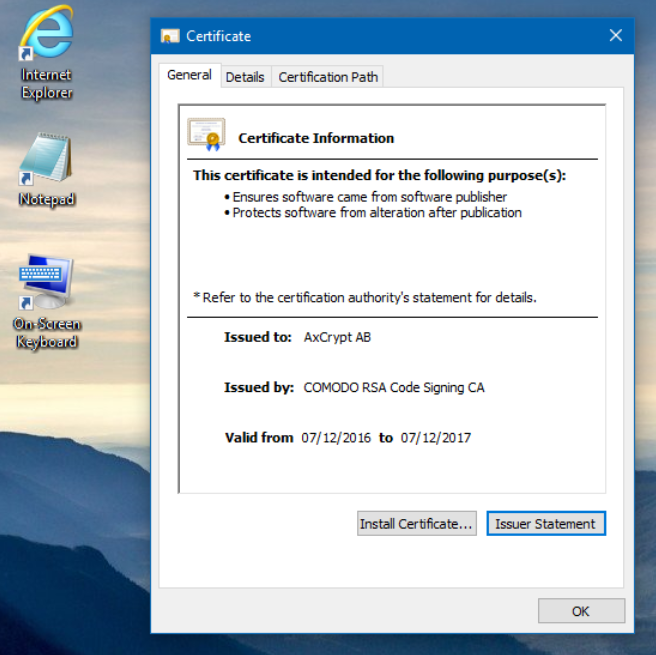
The correct current setup shows the following under ‘Details’:
AnonymousI asked Bitdefender for tech support and they said they block untrusted executable files from running if they’re not trusted by Windows Smartscreen. They said that Smartscreen intercepts suspicious files first and then the antivirus blocks any attempts to run it. I’m not a very technical user but I think I understand what has happened.
I downloaded my Axcrypt self decrypt backup from Google Drive onto my Windows 7 computer when a friend suggested I do that and it worked on there. I then copied the files onto a USB and onto my Windows 10 computer and it worked :)
I’ve sent the screenshot that you asked for.
When I was speaking to Bitdefender they asked me to email them a copy of that file for analysis. I asked a technical friend about Windows Authenticode and he said that it’s not difficult for people to obtain fake certificates or modify rogue software to bear a real certificate. He said that a lot of software has asc/has signatures and I should check these instead.
I can’t remember where I downloaded it from but it was probably Filehippo or CNET because the download on here wasn’t working and kept redirecting me. The Axcrypt website download is working now and I have all my files back I’m pleased to say.
Thanks for helping me.
Hello,
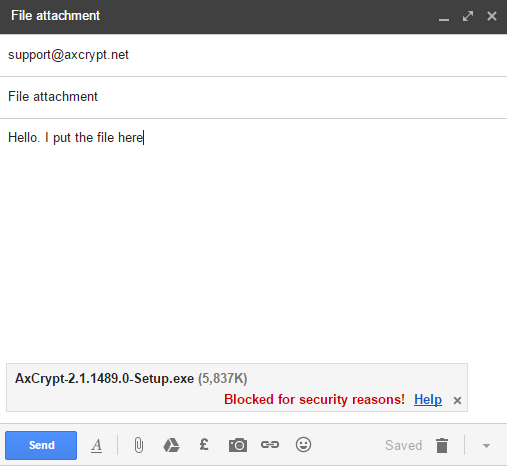
Can you please send the actual setup file with the January 5 timestamp to me at support@axcrypt.net ? You may need to copy it to a new name, and change the .exe-extension (I usually add “.removeme” for example), as email software often blocks .exe files.
Mariannethis is worrying.
i downloaded axCrypt from TUCOWS and my date is janury 5 as well.
here’s the picture from my screen and the certificate.
Hello Marianne (and anyone else seeing a download signed on January 5),
I can’t find AxCrypt 2 on Tucows at all. I only find a completely outdated version 1.5.
Can anyone who has the installer dated January 5, please either send a copy to support@axcrypt.net, or post a download link here so we can examine the file?
CyrilI don’t have this problem, I’ve double checked my installation file, but I agree with Adam that Authenticode does have problems.
Research Papers
https://software.imdea.org/~juanca/papers/malsign_ccs15.pdf
There are other papers out there. Really AxCrypt should be publishing the SHA256 sum of the software in addition to Authenticode considering the importance of maintaining the integrity of encryption software.
Hi Cyril,
Thanks for the links.
The first paper, https://software.imdea.org/~juanca/papers/malsign_ccs15.pdf does not actually say anything about Authenticode signatures being weak or possible to manipulate. It says that computer system implementers (i.e. Microsoft), are not using it properly, not detecting situations that Authenticode indicates – in this case revoked certificates.
I should of course also point out that Authenticode as such, does not say *anything* about the code, if it’s good, if it’s bad or if it’s ugly. It only strongly identifies the publisher, and make a strong statement that what you’re getting is what the publisher intended. If the publisher intends to publish malware, that can of course be signed. If this does happen, the idea with Authenticode is that you should then at least know who to sue or report to the police.
The second paper is interesting, and actually does to a certain extent demonstrate a weakness in the Authenticode implementation – they show they can *add* (not modify) arbitrary content while maintaining a valid signature. However, I’m actually at a loss to understand what they could *do* with this data, which the paper points out. Then it goes on to demonstrate an in-memory PE loader, which is also interesting – but to be honest, I don’t see how the one connects to the other. You still need to get that PE loader running. I guess you could write a software, include the PE loader, sign it – and then after that add the ‘payload’ as described but I don’t see the threat yet here. Then again – attacks never get worse, they only get better.
Thanks for two interesting reads! I don’t think it reduces trust in Authenticode as a signing mechanism from a known publisher (AxCrypt AB in this case) though.
We could certainly publish hashes of our executables, it doesn’t harm anything. I’m making a note of it, but since we don’t want any manual processes for stuff like that, we’ll need to add a few things to our platform so we can publish them automatically.
I still really, really want to get my hands on a sample of the file that seems to be signed January 5 and sort out what that is about. Probably its nothing, but we want to investigate.
AlejandroHi Moderators!
I use AxCrypt and I was looking to find out about the self decrypt feature. Then I find this topic.
I use the instructions to check certificate and mine is dated 04 January 2017. Is this wrong? Mine came up with a smartscreen warning and I followed instructions to clear it.
http://es.ccm.net/faq/9349-como-desactivar-windows-smartscreen-en-windows-8
I have gone to send it to the support email but my email is not permitido. I tried changing the extentsion but Im still being blocked.
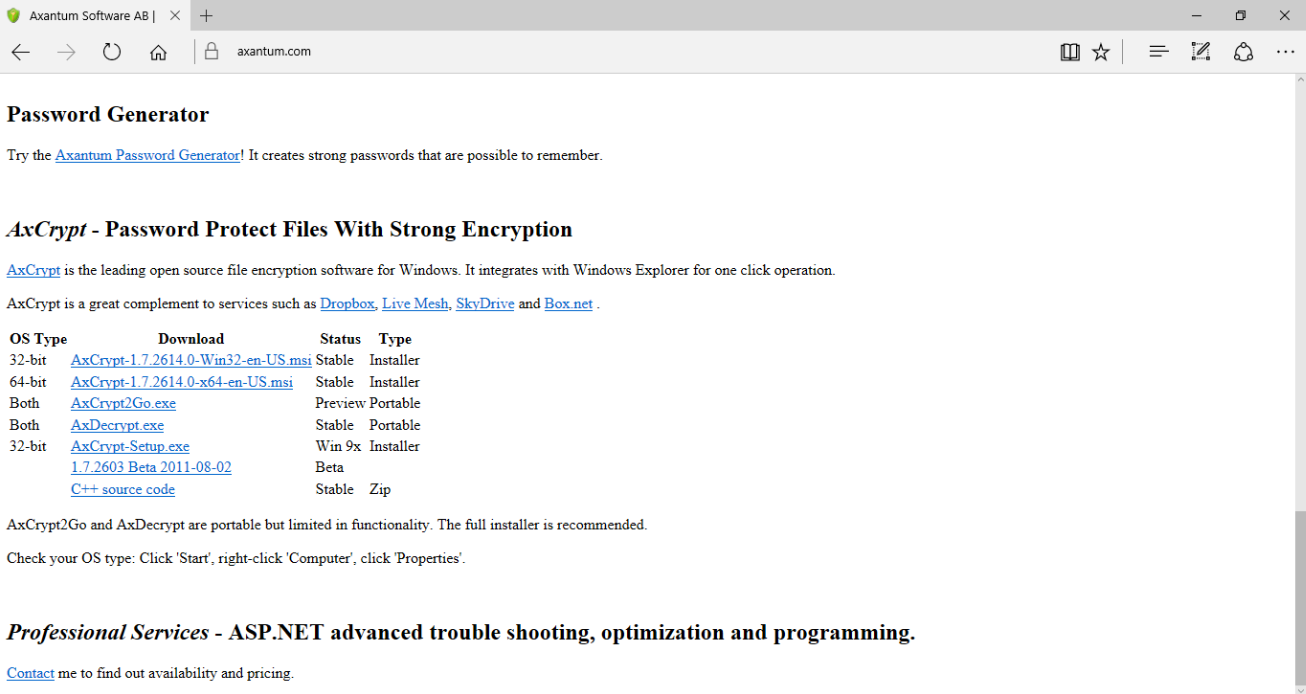
Here are fotos of my email and website I download AxCrypt from.
Hello Alejandro,
Yes, some mail softwares (gmail notably) will not be fooled by the extension trick.
Please use AxCrypt to encrypt it, and then key share it with ‘support@axcrypt.net’ and then send the encrypted file.
Or, upload it to dropbox, Google Drive or similar and then share it with ‘support@axcrypt.net’.
Also, that website… That does *not* look like http://www.axantum.com/ . This is what it looks like:
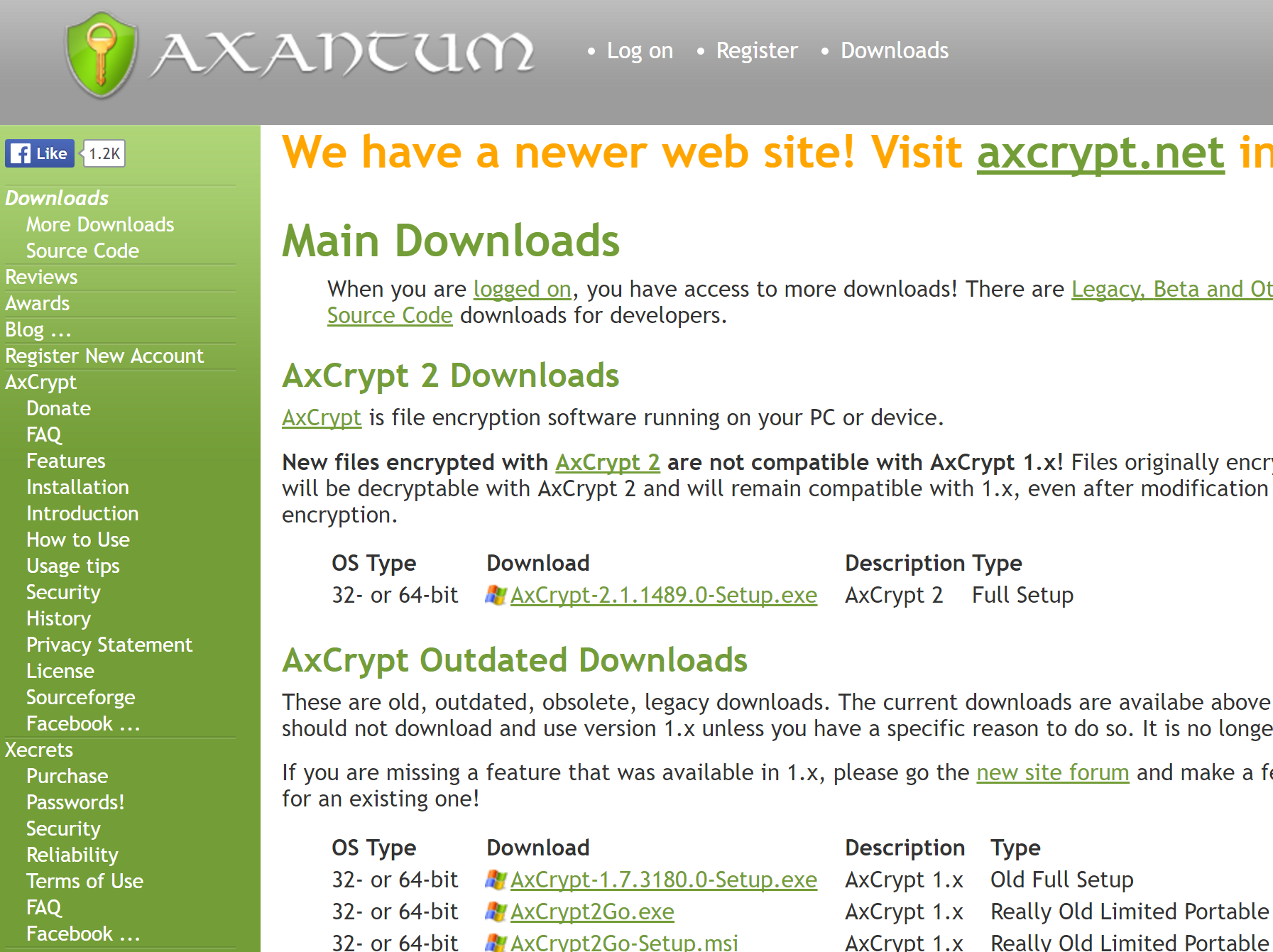
MarcoI have this same problem. My virus scanner is not letting me run the AxCrypt 2 download. The certificate date is 5JAN17 and I am in Zurich.
Instead I have to download AxCrypt-1.7.3180.0-Setup.exe from the forum link and this works perfectly. I have deleted the unsafe AxCrypt2.
https://forum.axcrypt.net/forums/topic/axcrypt-2-0-and-1-7/page/7/
The certificate date is 4JUL16 and I believe this is the real software.
The SHA1 is – a9fac97c1ed306690abfb90b03331482c82c91ae and MD5 is – 3156d97c3fcce2e2edaa3468755be806.
Hello Marco,
Please! Send a link to where you downloaded the file, and also send the actual file to support@axcrypt.net . We cannot investigate this unless we can see what you see.
Also, it’s not easy to know exactly what you’ve downloaded since we don’t know where or what, but the correct hashes of ‘AxCrypt-2.1.1489.0-Setup.exe’ is:
MD5: ca117875db4cd0c011132c782957f248
SHA1: 9f8a0688008c0969d1edb639af81e3205458d692
SHA256: 8c6856038c15ff231e66521fc4cef210226083b6b134de64e36b31f149b22b48The correct hashes for ‘AxCrypt-1.7.3180.0-Setup.exe’ is indeed as you report Marco (but we’re really more interested in getting a sample of a ‘bad’ file than a ‘good’ file):
MD5: 3156d97c3fcce2e2edaa3468755be806
SHA1: a9fac97c1ed306690abfb90b03331482c82c91ae
SHA256: 6a075e415a3c98e835997d0896aab2da5ba0565bd2bf4a6a7a05afdd8c25870aSo, folks, can anyone with a file not matching the above – especially a AxCrypt-2.1.1489-Setup.exe with a digital signature timestamp that is in January 2017, please provide us with a sample and/or a URL where the file was downloaded from?
-
AuthorPosts

